
IT & Information-Security Governance
We advise clients in defining and implementing cyber security and privacy governance and management frameworks that help them to secure their information assets and align their IT and Information-Security function to their business objectives.
Our IT & Information-Security Governance Services align with the following leading frameworks

NIST Cyber Security Framework (NIST 800-53):
The Framework was established by National Institute of Standards & Technology (USA). It provides a management framework for Cyber Security and for how organizations can identify, prevent, detect respond and recover from cyber attacks.
COBIT:
This is an IT management framework developed by the IT Governance Institute and ISACA.
ISO 20000:
This is the first international standard for governance of IT Service Management (ITSM). This standard, developed in 2005, encapsulates the best practices encapsulated within the ITIL (information technology infrastructure library) framework. It also includes practices from Microsoft Operations Framework and elements from ISACA’s COBIT framework.Our Governance Services Include









Risk Management:
Risk is the possibility or likelihood that a threat will exploit a vulnerability to cause harm to an asset. Our Risk Management practice is aimed at preventing loss or disclosure of data and IT asset while sustaining authorized access and maintaining a secured IT environment.
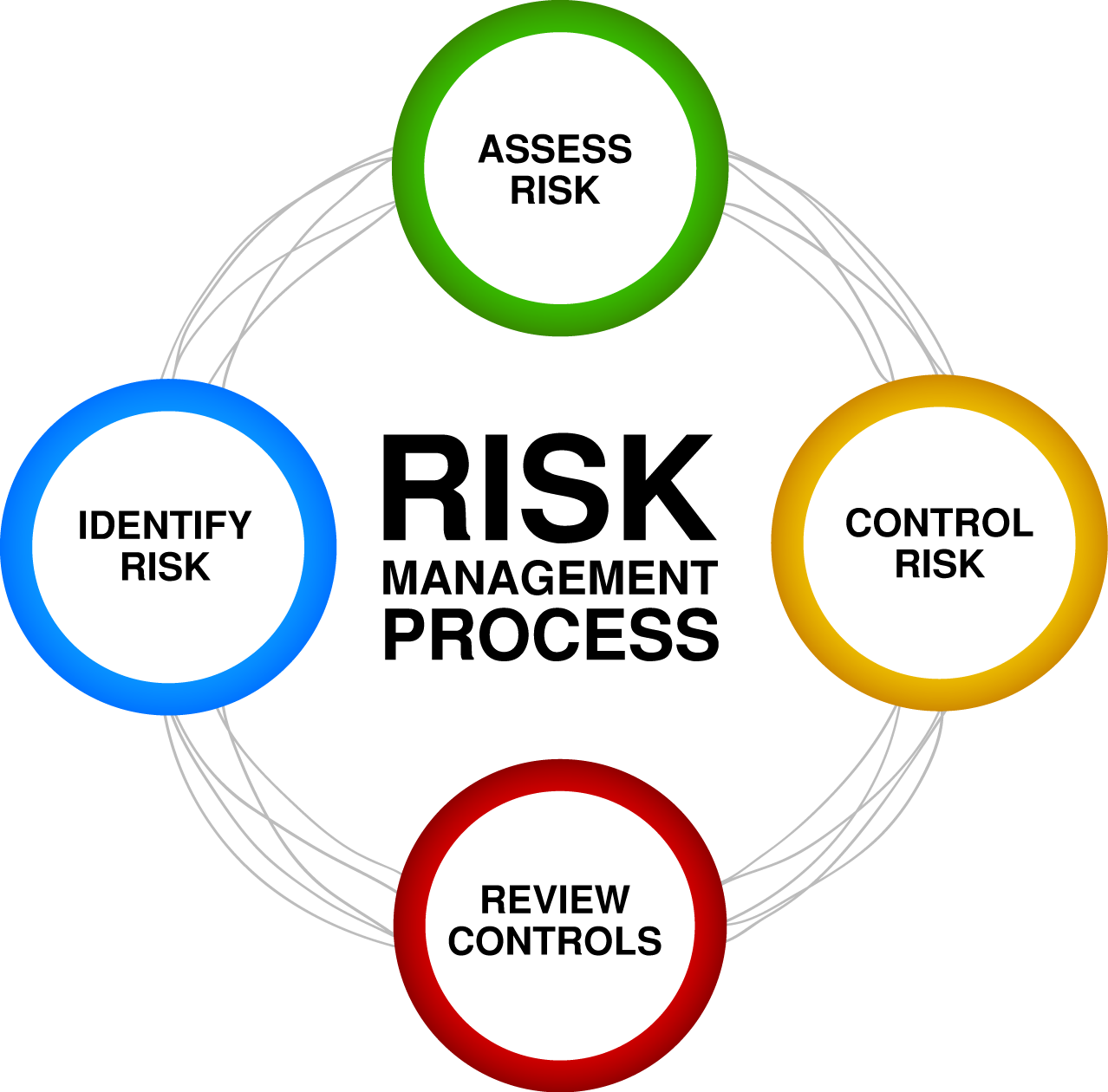
Our Risk Management Services include the following:

Risk Identification:
Identifying, inherent and external, threats and vulnerabilities (e.g. Viruses, Criminal Activities, Internal Threats, Disgruntled Employees, Unauthorized Access etc) which could lead to damage or unauthorized disclosure of data, software applications and other IT infrastructure assets in your enterprise.
Quantitative Risk Analysis:
Estimating Asset Value, Calculating Exposure Factor, Calculating Single Loss Expectancy, Assess Annualized Rate of Occurrence, Derive Annualized Loss Expectancy, Perform Cost / Benefit Analysis of Countermeasures or Safeguards (often also referred to as ‘Controls’)
Qualitative Risk Analysis:
By use of Delphi Techniques, Surveys, Focus Groups, Questionnaires, Interviews etc.
Risk Reporting:
Based on our assessment and analysis we provide a comprehensive report to the management based on which management can take decision on countermeasures and Risk Mitigation strategies. Our report consists of the following:- Complete & detailed valuation of all assets
- An exclusive list of all threats and risks, rate of occurrence and extent of loss if threat is realized.
- A list of threat-specific safeguards
- A cost-benefit analysis of each safeguards.

Risk Mitigation:
We provide clients detailed advice on Risk Mitigation and provide necessary services for implementation of Risk Control Measures.Compliance
Compliance is the act of conforming to or adhering to rules, regulations, standards, contractual norms or requirements of an industry as is laid down by government regulators and/or industry associations or trade organizations.
We provide Advisory and Implementation Services for the following Frameworks, Laws and Regulations.














